~ First Batch of Catalog ~
Following shortly China’s New Cybersecurity Law, the Cyberspace Administration of China (CAC) announced a Catalog of the equipment subject to security review. Despite being published on the 9th of June 2017, this catalog has been attached to the law as an appendix dated on the 1st of June, therefore taking effect on same date as the promulgation of the law.
The publication of the catalog follows what Article 23 of the Law mentioned, stating that “critical network equipment and specialized network security products shall follow the national standards […], and be safety certified […] before being sold or provided”. For that purpose the article indicates that the State Council has the mission to “formulate and release a catalog of critical network equipment and specialized network security products”.
This mission has now been partly fulfilled with the publication of the first batch of devices listed in the catalog, that should be completed over the coming months with additional batches.
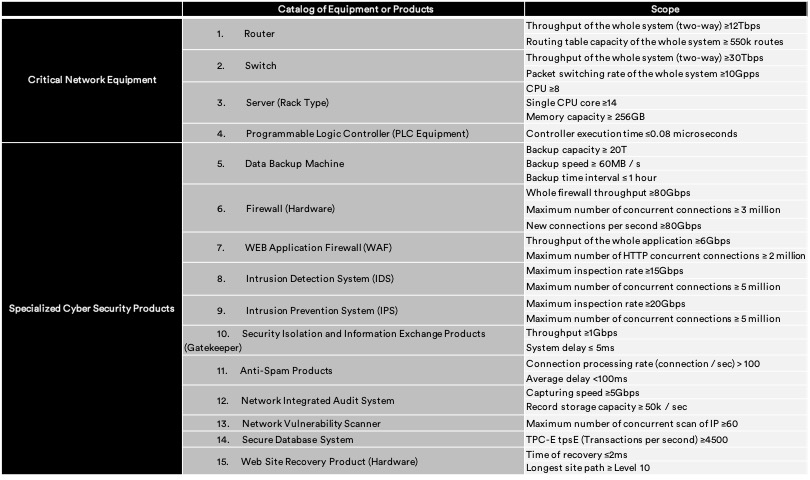
The content of the first list indicates more clearly the domains China’s authorities are focusing their interest on to regulate and control. It identifies 15 products under two categories: Critical Network Equipment and Specialized Cyber Security Products.
These products should pass:
- a “security examination” from an unidentified qualified institution, and – if compliant – be registered to the Ministry of Industry and Information Technology and the Ministry of Public Safety of the People’s Republic of China, or
- a “security certification” from a qualified institution which should report the result to the Certification and Accreditation Administration.
Should a product fall under a class, it is also interesting to note the minimal technical specifications of each device have been included in the catalog. As an example, to be subject to legal Security Audit a Router needs to have a “Throughput of the whole system (two-way) ≥ 12Tbps” and/or a “Routing table capacity of the whole system ≥ 550k routes”. Therefore many products with modest technical capabilities can escape the constraints of the law.
The complete list of equipment can be found here below, translated for reference only.
For further information, please contact:
Gregory Louvel – g.louvel@leaf-legal.com