Effective since 1st of June, 2017, Cybersecurity Law (“CSL”) of the People’s Republic of China (“China”) places itself as an overarching regulatory framework to cover all cybersecurity matters from network security, data privacy, to data storage and transfer.
Although the CSL provides significant sanctions – corporate fines up to USD 1,4M and personal sanctions including imprisonment – it does not benefit from a crystal clarity regarding implementation measures, leaving data controllers in a precarious position.
This newsletter lists the major 3 steps a data controller must follow to achieve maximum compliance in China.
1. IDENTIFICATION
Mapping of data flow
From its creation to its destruction, data will go through life stages, such as collection, storage, processing, transfer, sharing, archive, destruction. Some stages can also happen outside the data controller’s direct control in case of tasks outsourced to third-party providers.
Every stage requires a clear identification articulated on a data flow map. This map will become the base to further analyse pain points.
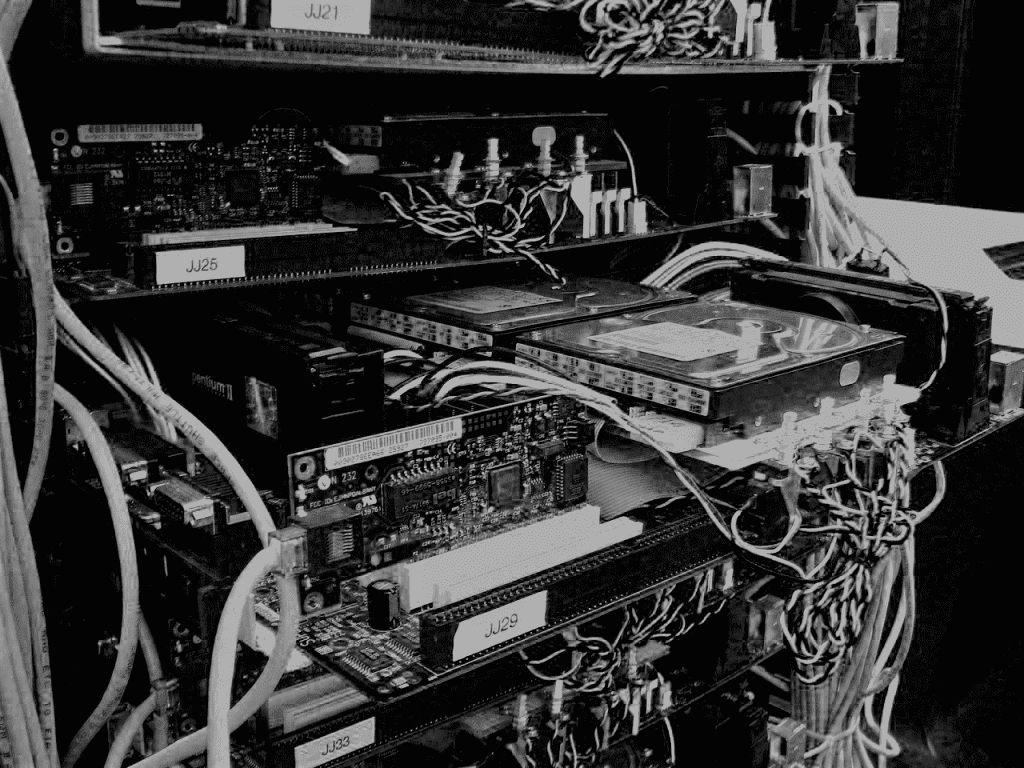
Audit of network protection
Every data life cycle presents weak points either from an external standpoint because of poor network security, or an internal standpoint because of inadequate staff permission strategy.
Running a full spectrum audit including penetration testing will identify heat points to be addressed as priorities.
Assessment of legal liabilities
Legal liabilities may arise from several heat points on the “data life cycle map”, the most common ones being the lack of compliant privacy policy, user request processes, network security measures and data breach response plan.
2. MITIGATION
Update of data privacy process
The privacy policy shall not only be comprehensive, but also written in a clear manner, taking into consideration data subject technical level of understanding and profile.
This key document serves as a guide for the user to understand key information such as: data collected, lawful basis, collection and processing purposes, user’s right on access, modification, erasure, portability, and communication channels with the company.
The privacy policy shall also be integrated in a seamless fashion to avoid disrupting users’ experience.
Control of third-party induced liabilities
As the privacy policy represents the “front end” of data privacy, the “back end” shall also reflect the policy through internal process regarding users’ rights such as data access, rectification, erasure and portability.
A customer support shall be implemented to receive, treat and archive user’s requests in a timely manner and for free or at cost.
As data controllers generally outsource a major scope of customer relationship management, network security and data processing, regulations also include such practices and hold accountable the organisation for any violation caused by third parties. It appears therefore critical to review and update third party contractual documentation to reflect and anticipate such liabilities.
In the turmoil of a data breach, there is no time to decide what strategy to adopt, what staff or providers should be responsible, what tasks should be prioritized: there is only time for execution.
3. PLANNING
Data breach preparedness plan
A data controller should define, implement and test a comprehensive plan to prepare for the worst-case scenario: a data breach, or “a violation or imminent threat of violation of computer security policies, acceptable use policies, or standard security practices”.
The response to such data breach relies on a systematic approach in 4 stages:
Preparation, Detection & Analysis, Containment Eradication and Recovery and finally Post-incident Activities.
Incident response team
The incident response team is constantly preparing and will be deployed upon detection of a data breach. The team is comprised of personnel from various department within the organisation – including C-level executive, such as the Data Protection Officer – and outsourced experts – such as legal counsel and forensics. With clearly defined roles, the team members will be able to address every situation in a comprehensive and planned manner.
The incident response team holds a central role in the communication with other stakeholders as illustrated below, to assure a smooth execution of the data breach plan, observe a comprehensive approach, and deliver a consistent message.
Training
Human error is the leading cause of data breach, and may be addressed by a continuous training across the entire organisation. Although IT staff members are usually more rounded to security protocols, any staff member can be targeted as a point of failure for hackers to gain access to the entire organisation’s network and data.
An organisation raising awareness and implementing good practices across its entire staff will become more resilient to incidents compared to an organisation only training IT staff.
A comprehensive training will include updates on regulation and technologies, monitoring of breaches, workshops, and periodic drills. Good practices will include password management, connexion to public and corporate network, physical access security to facilities, internal and external data sharing, identification verification, use of approved tools, and documentation of incident or near-misses. The main goal is not simply to lower the risk of breach, but also to promote and invigorate a corporate culture around data security and privacy.
Privacy and protection by design
With structural implications of cybersecurity and privacy regulation at every stage of the data life cycle, data controllers gradually integrate compliance from the creation of their solution. Although not as explicit as in the EU, privacy and protection by design is an emerging concept in China and deserves a close attention from data controllers. Such approach will remove liabilities and prove more agile upon scaling the business.